The PIC18F2680 MCU employs code protection mechanisms that secure the firmware, preventing direct access or duplication. The secured program memory is designed to resist traditional copy and dump techniques. However, in cases where firmware recovery or replication is needed, advanced attack strategies are utilized.
Methods to Break Microchip PIC18F2680 Firmware Protection
-
Firmware Dumping & Extraction
-
Using specialized equipment to dump the binary file from the flash memory.
-
Bypassing security bits to copy the program from the chip.
-
-
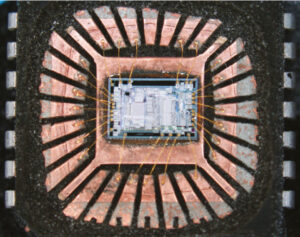
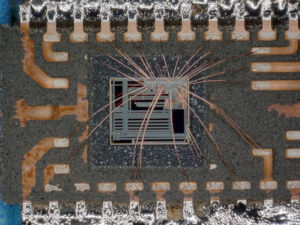
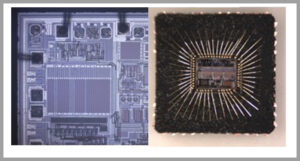
Decapsulation & Physical Attacks
-
Exposing the microcontroller die to extract data directly.
-
Optical and scanning electron microscopy to access the protected source code.
-
-
Decrypting Encrypted Data
-
Applying cryptographic analysis to recover the locked firmware archive.
-
Using side-channel attacks to gather information from the secured MCU memory.
-
Why Choose Professional Services?
Extracting or cloning the PIC18F2680 firmware requires expertise in microcontroller attack techniques. Our specialists ensure precise and efficient firmware recovery while maintaining the integrity of the program file. If you need to replicate or decrypt a locked MCU, contact us for professional assistance.
Сброс и извлечение прошивки
Использование специализированного оборудования для сброса двоичного файла из флэш-памяти.
Обход битов безопасности для копирования программы из чипа.
Декапсуляция и физические атаки
Вскрытие кристалла микроконтроллера для непосредственного извлечения данных.
Оптическая и сканирующая электронная микроскопия для доступа к защищенному исходному коду.
Расшифровка зашифрованных данных
Применение криптографического анализа для восстановления заблокированного архива прошивки.
Использование атак по сторонним каналам для сбора информации из защищенной памяти микроконтроллера.
The Idle modes allow the controller’s CPU to be selectively shut down while the peripherals continue to operate to faciliate the process of Read Protected Microchip PIC18F2680 Eeprom Content. Selecting a particular Idle mode allows users to further manage power consumption. If the IDLEN bit is set to a ‘1’ when a SLEEP instruction is executed, the peripherals will be clocked from the clock source selected using the SCS1:SCS0 bits; however, the CPU will not be clocked.
Dumping & Extragere Firmware
Utilizarea echipamentelor specializate pentru a descărca fișierul binar din memoria flash.
Ocolirea biților de securitate pentru a copia programul de pe cip.
Decapsulare și atacuri fizice
Expunerea matriței microcontrolerului pentru a extrage datele direct.
Microscopie optică și electronică de scanare pentru a accesa codul sursă protejat.
Decriptarea datelor criptate
Aplicarea analizei criptografice pentru a recupera arhiva firmware blocată.
Utilizarea atacurilor pe canale laterale pentru a aduna informații din memoria securizată a MCU.
The clock source status bits are not affected. Setting IDLEN and executing a SLEEP instruction provides a quick method of switching from a given Run mode to its corresponding Idle mode. If the WDT is selected, the INTRC source will continue to operate. If the Timer1 oscillator is enabled, it will also continue to run when Read Protected Microchip PIC18F2680 Eeprom Content.
Since the CPU is not executing instructions, the only exits from any of the Idle modes are by interrupt, WDT time-out or a Reset. When a wake event occurs, CPU execution is delayed by an interval of TCSD (parameter 38, Table 22-10) while it becomes ready to execute code. When the CPU begins executing code, it resumes with the same clock source for the current Idle mode.
Ürün Yazılımı Dökümü ve Çıkarımı
Flaş bellekten ikili dosyayı dökmek için özel ekipman kullanma.
Programı çipten kopyalamak için güvenlik bitlerini atlama.
Kapasülasyon ve Fiziksel Saldırılar
Verileri doğrudan çıkarmak için mikrodenetleyici kalıbını açığa çıkarma.
Korunan kaynak koduna erişmek için optik ve taramalı elektron mikroskobu.
Şifrelenmiş Verilerin Şifresini Çözme
Kilitli ürün yazılımı arşivini kurtarmak için kriptografik analiz uygulama.
Güvenli MCU belleğinden bilgi toplamak için yan kanal saldırıları kullanma.
For example, when waking from RC_IDLE mode, the internal oscillator block will clock the CPU and peripherals (in other words, RC_RUN mode). The IDLEN and SCS bits are not affected by the wake-up. While in any Idle mode or the Sleep mode, a WDT time-out will result in a WDT wake-up to the Run mode currently specified by the SCS1:SCS0 bits before Read Protected Microchip PIC18F2680 Eeprom Content.

