Maintaining and analyzing embedded systems is vital. Our advanced service to decode secured Microchip MCU PIC18F2682 firmware provides clients with an in-depth evaluation of their devices while ensuring complete adherence to legal and ethical standards. This service is specifically designed for those with rightful ownership or explicit authorization, assisting in critical tasks such as firmware recovery, legacy system replication, and security auditing.
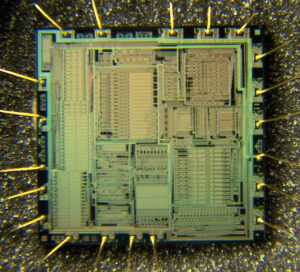
The PIC18F2682 microcontroller is renowned for its robust security measures. Its firmware is intentionally secured, protected, and encrypted to prevent unauthorized access. However, even the most locked and safeguarded chips may require analysis for maintenance or upgrade purposes. Our specialized process employs a suite of advanced techniques including reverse engineering, decrypting, and controlled extraction. We carefully crack and decapsulate the chip package in a laboratory setting, using non-destructive methods to dump the binary data stored in the flash and EEPROM memories.
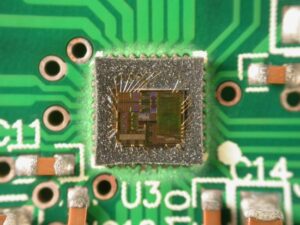
The procedure begins with a comprehensive evaluation of the chip’s architecture and memory layout. Our engineers then attack the secured firmware with state-of-the-art tools designed to extract and copy the embedded program without compromising the integrity of the microprocessor. Techniques such as hacking and decapsulation are applied in a controlled environment to extract the firmware archive. Once the binary data is dumped and recovered, our team employs reverse engineering methods to replicate the source code structure and analyze the data. This process not only facilitates the cloning of legacy systems but also ensures that any subsequent program updates or security enhancements are built on a thorough understanding of the original firmware.

Moreover, our service ensures that every step—from the initial extraction to the final decryption of the locked firmware—is documented and performed with meticulous precision. This enables our clients to obtain a clear, detailed overview of the program’s structure, whether they need to replicate a critical component or conduct an in-depth security assessment. By offering the ability to extract and recover essential firmware data, we empower clients to safeguard their technology assets and innovate with confidence.
In summary, our decode secured Microchip MCU PIC18F2682 firmware service harnesses techniques such as crack, attack, decapsulate, hack, decrypt, copy, and reverse engineering to provide a comprehensive, legally compliant solution. This unique approach addresses the specific characteristics of the PIC18F2682 chip and delivers unparalleled insights into its internal architecture—ensuring that every firmware, source code file, and memory archive is accurately replicated and analyzed for enhanced performance and security.
This mode is unique among the three low-power Idle modes, in that it does not disable the primary device clock. For timing sensitive applications, this allows for the fastest resumption of device operation with its more accurate primary clock source in the process of Decode Secured Microchip MCU PIC18F2682 Firmware, since the clock source does not have to “warm-up” or transition from another oscillator.
PRI_IDLE mode is entered from PRI_RUN mode by setting the IDLEN bit and executing a SLEEP instruction. If the device is in another Run mode, set IDLEN first, then clear the SCS bits and execute SLEEP. Although the CPU is disabled, the peripherals continue to be clocked from the primary clock source specified by the FOSC3:FOSC0 Configuration bits. The OSTS bit remains set when Decode Secured Microchip MCU PIC18F2682 Firmware.
When a wake event occurs, the CPU is clocked from the primary clock source. A delay of interval TCSD is required between the wake event and when code execution starts. This is required to allow the CPU to become ready to execute instructions of Copying Microchip PIC16F87 Code. After the wake-up, the OSTS bit remains set. The IDLEN and SCS bits are not affected by the wake-up.
In SEC_IDLE mode, the CPU is disabled but the peripherals continue to be clocked from the Timer1 oscillator. This mode is entered from SEC_RUN by setting the IDLEN bit and executing a SLEEP instruction. If the device is in another Run mode, set the IDLEN bit first, then set the SCS1:SCS0 bits to ‘01’ and execute SLEEP. When the clock source is switched to the Timer1 oscillator, the primary oscillator is shut down, the OSTS bit is cleared and the T1RUN bit is set to facilitate the process of Extract Microcontroller PIC16C710 Code.
When a wake event occurs, the peripherals continue to be clocked from the Timer1 oscillator. After an interval of TCSD following the wake event, the CPU begins executing code being clocked by the Timer1 oscillator. The IDLEN and SCS bits are not affected by the wake-up; the Timer1 oscillator continues to run when Crack MCU.

